There won't be any leaks from the OWCD data backup, right?
Data Diode OWCD Series
Is there no risk of backup storage data leaking? It's also important to have a system in place that prevents data from being stolen.
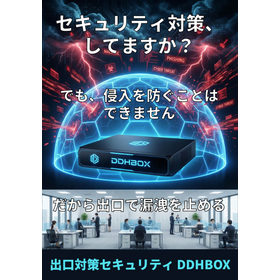
Ransomware encryption and information leaks are occurring one after another. "Backup in a separate environment, immutability, and recovery testing" are listed as essential measures to take against ransomware. The intrusion routes are diverse, including email, web, social media, and VPN devices, and the risk increases as the use of the internet grows with the spread of generative AI. Once breached, recovery can take days, during which business operations may come to a halt. Quick recovery requires a data backup that combines both online and offline methods. Backups are the most critical assets; when they are accessible externally, they become prime targets for attackers. Let's avoid large-scale damage by cutting off unnecessary communication paths. OWCD can protect against poor outcomes by making the backup environment a "one-way channel for sending data to be stored," thereby blocking information leaks obtained by ransomware. ➡ Adopted as a technology to enhance the "separation of backups: storing in different segments." While having OWCD does not solve everything, the way it is implemented can significantly enhance defensive capabilities. Please consider it. For inquiries, please visit the related link below. There is an explanatory video available.
Inquire About This Product
basic information
Place the OWCD on the data arrival route and control it so that communication can only occur in the "incoming" direction. Viruses send their location information and value judgments to external sources via remote operators, but if that communication is blocked by the OWCD, no further data will be sent out. Of course, this also prevents the leakage of important information. The OWCD has a special structure that allows communication signals to flow in only one direction. In this application, it is restricted to "incoming" only, blocking external leakage. At first glance, the incoming side may seem defenseless. However, the OWCD cannot allow common office communications (TCP/IP) to pass through, and this characteristic can be utilized to perform filtering just before protocol conversion, making it easy to combine with existing virus check functions. Even though it appears simple, by establishing a checkpoint, the boundary of responsibility is clarified, and data can be reliably verified to enhance safety. Business leaders, please take a look at the incidents occurring now. The longer business interruptions last, the more revenue and trust are lost. While the introduction of the OWCD requires initial investment, it represents a significant step forward in strengthening defenses without incurring operational labor costs. For inquiries, please contact us through our company website above.
Price information
There are no longer any measures that cannot be breached by software. OWCD is also highly compatible with zero trust. Implementation support is available. By adding physical barriers and layering, we can enhance business continuity and resilience through damage limitation. If business interruptions prolong, not only revenue but also trust will be lost. OWCD is a cost-effective option for cyber resilience measures that can enhance defense capabilities without incurring operational labor costs. We encourage SIers to consult with us as well. Please contact us through our company website mentioned above.
Price range
P5
Delivery Time
※We are engaged in made-to-order production. Please contact us through our company website mentioned above.
Applications/Examples of results
Government Agency Information Systems (Communication Backflow Control for Incoming External Emails) Traffic Information Systems (One-Way Communication Control from Control Systems to Public Web Servers) Remote Monitoring Systems for Industrial Equipment (Intrusion Prevention at Data Transmission Units) Supply Chain Information Collection Systems in Industry (Prevention of Unauthorized Intrusions into Production Facilities and Unauthorized Data Exfiltration at Collection Points) Core Information Management Systems in Research Institutes (Prevention of Intrusions into Research Facilities and Prevention of Unauthorized Data Exfiltration from Data Servers) While there are many large systems, the use is also expanding among medium and small enterprises, starting with file management and IoT equipment status monitoring. As mentioned above, in addition to government agencies, power plants, manufacturers' research institutes, and production information dissemination points, IoT information dissemination, we are also utilizing it in defense systems. In today's digital society, intrusions can occur from anywhere. The resilience to notice and begin addressing issues at the early reconnaissance stage is essential. Let’s protect against reaching the core. The number of users is steadily increasing, and we will also provide guidance on applications for special uses such as remote maintenance. Please make the most of it. For inquiries, please contact us via our company website above.
catalog(4)
Download All CatalogsCompany information
Our company is a member of the Mitsubishi Heavy Industries Group, serving as a design technology partner for Mitsubishi Heavy Industries, where we engage in planning and mechanical design for prime movers (steam turbines/boilers, gas turbines, water turbines), pumps, and various plants, as well as instrumentation control system planning and electrical design. In order to meet the increasingly diverse and sophisticated needs of our customers, we will continue to challenge ourselves to improve our technological capabilities, streamline operations, and reduce costs based on the trust we have built with users. Through this, we are developing activities that contribute to society by providing the products and engineering capabilities we have cultivated so far to everyone. Alongside the sale of products related to IoT, manufacturing DX, and on-site monitoring/condition monitoring, we will focus on custom orders, customization, and system construction to realize your ideas. We encourage you to consider utilizing our services. https://eng.power.mhi.com










![[Presentation of Materials] You can learn the basics of wireless engineering and wave propagation easily!](https://image.mono.ipros.com/public/product/image/18e/2001524556/IPROS2929987369746077914.jpg?w=280&h=280)